Expect the Unexpected: Exploring Multidisciplinary Approaches to Insider Threat Mitigation
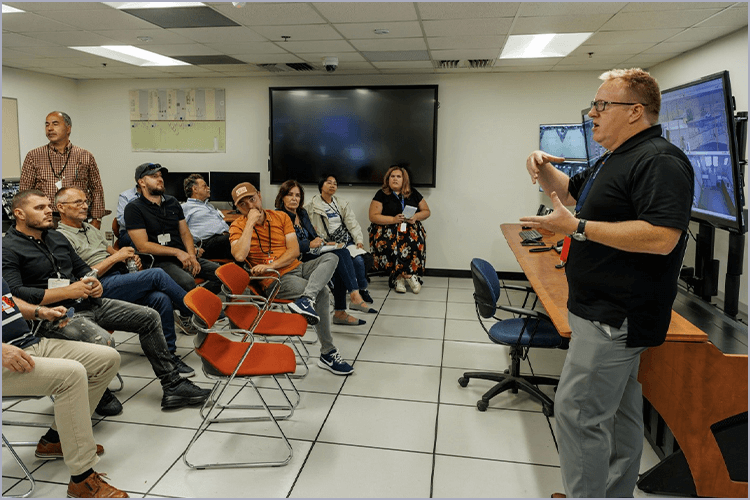
Bringing together our international community of practice, the three-day symposium with approximately 200 participants featured engaging panel discussions, interactive sessions, and networking with practitioners.
The purpose of the symposium was to showcase meeting commitments per the 2016 Joint Statement on Mitigating Insider Threats (INFCIRC/908) while developing and fostering an integrated insider threat mitigation community for the nuclear security domain. With more than 30 countries and INTERPOL subscribed to INFCIRC/908, the International Symposium on Insider Threat Mitigation is a critical forum for discussion, action, and collaboration.
2024 Agenda
Tuesday, March 5, 2024
Setting the Stage: INFCIRC/908 Since 2016 and Today's Challenges
Time
Topic
0830-0930
Registration
0930-0945
Logistics & Housekeeping Logistics, safety, and first aid discussion
0945-1015
This session provided an overview of INFCIRC/908 initiatives from 2016 to present with strong emphasis on developing the insider threat mitigation community of practice.
1015-1030
Presentation of certificates to current INFCIRC/908 Steering Committee members
1030-1105
Coffee Break: Press Moment
1105-1115
Opening Remarks + Photo Opportunity The opening remarks highlighted the importance of nuclear security and insider threat mitigation.
1115-1200
Emerging Issues Panel Discussion Emerging technologies and global conflicts present both risks and opportunities for nuclear security practitioners. In this plenary session, participants explored the risks and benefits of nuclear security measures, particularly the mitigation of insider risks.
1200-1245
Nuclear Regulator Roundtable Regulators/competent authorities and law enforcement representatives explored innovative approaches to strengthening legal frameworks to support nuclear security. Lessons learned from nuclear security incidents were shared in the form of recommendations.
1245-1345
LUNCH SESSIONData-Driven & Risk Significant: Demonstrating a New Approach to Insider Threat Detection and Mitigation for Nuclear Facilities
1245-1345
Concurrent Sessions 1
1345-1435
Policy & Regulations: Stakeholders and Success Stories (Panel)Panelists discussed how their organizations identify and engage stakeholders to develop and then evaluate ITM programs. Topics included establishing relationships with key stakeholders, developing program metrics, securing buy-in from executives, and measuring the ROI of financial investments (e.g., staffing, procuring, and deploying security systems). Panelists shared success stories with the audience.
1345-1435
Mitigating Radioactive Source Threats in the Transportation Sector (Panel)Panelists tackled the tough topic of how to mitigate insider threats to the transportation of radioactive material. Topics included best practices for mitigating insider threats in the transportation sector, the intersection of transportation security and other security concerns like physical protection, future trends in the industry, the role of self-driving cars, artificial intelligence, and cyber threats. Panelists took questions from the audience.
1345-1435
Panelists reflected on Focus Group findings from a survey distributed to INFCIRC/908 Subscribing Member States. Different approaches to establishing trust and reliability in an organization were be described. Audience members shared their personal experience and reflections on the survey results.
1345-1435
This panel discussion assembled experts from the nuclear and radiological industry, each having insights into the challenges of social media vetting in high-security roles. Panelists shared firsthand accounts of their experiences with social media vetting, highlighting specific case studies.
1435-1445
Transition to Next Session
1445-1545
CONCURRENT SESSION 2 – Interactive Exercises
1445-1545
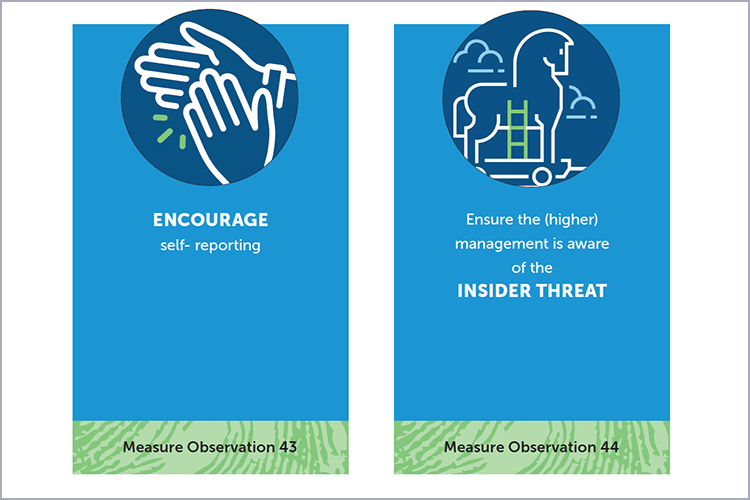
Participants with varied backgrounds shared their experiences and views, which provided an overview of prioritized red flags and measures in the topic of ‘observation’. The goal was to evaluate, in small groups, a set of red flags and measures and place them in different categories: high/medium/low and must-have/ nice-to-have/ not useful. This exercise is based on doctoral research. At the end of the exercise, participants reviewed and reflected on their choices as compared to the research. Note: The downloadable cards are to be printed 2-sided: Side 1: Observation, Side 2: Logo.
1445-1545
During this exercise, participants learned how an insider with cyber capabilities can negatively impact facility operations. Real world cases were examined to illustrate best practices to bolster security cybersecurity programs.
1445-1545
The nuclear power industry faces unique challenges with multinational workforces. On one hand, embracing diversity and multicultural teams can lead to dynamic and inclusive organizational environments. However, diversity can also amplify differences in security awareness, culture, vetting, and qualifications. To broadly address these differences and create baseline levels of security, a Nuclear Security Culture exercise addressed these concerns. The exercise identified unique cultural dimensions associated with nations and combined core components with a strong Nuclear Security Culture.
1445-1545
Do you know how to effectively collect information when a suspected insider threat incident has been reported? Techniques from motivational interviewing research were demonstrated to illustrate what works to reduce resistance and increase information collection.
1445-1545
This interactive, realistic scenario-based experience focused on enhancing awareness and implementing strategies to counteract insider threats enabled by cyber means. The session’s primary goal was to educate attendees about the criticality of recognizing and identifying risks, cross functional communication, and coordination between security domains to develop efficient strategies to mitigate these insider threats.
1545-1615
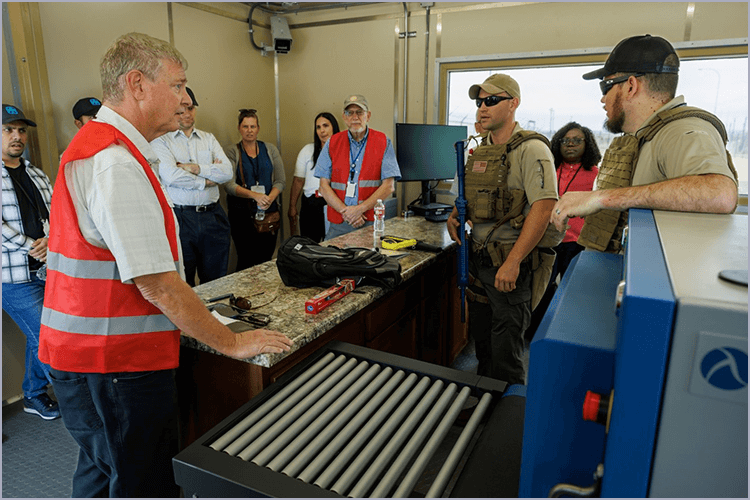
Coffee Break:ASK AN EXPERT SESSION 1: Physical Protection & Technical Measures Focus Group
1615-1715
Cross-Industry Perspectives on Mitigating Insider ThreatsPanelists from various industries addressed similarities and differences in mitigation strategies.
1715-1730
Day 1 Wrap-Up/Mentimeter
1730-1930
International Initiatives & Vendor ExpositionSelected organizations and vendors were available to discuss products, materials, and events germane to the insider risk/threat community.
1830
Reception
Wednesday, March 6, 2024
Post-pandemic Challenges; Current State of Practice
Time
Topic
0900-0915
Welcome; Recap of Day 1 and Preview of Day 2.
0915-0945
0945-1045
Mitigating Insider Threats in Times of Crisis Political, economic, and societal turmoil can each wreak havoc on nuclear security. Panelists shared their personal and professional perspectives on the strains imposed by such events as well as the steps taken to overcome challenges and increase organizational resilience.
1045-1115
Coffee Break & TransitionASK AN EXPERT SESSION 2: National Policy & Regulatory Frameworks
1115-1215
CONCURRENT SESSION 1 – Focus on Trustworthiness & Reliability, Cybersecurity, Physical Protection & Technical Measures
1115-1215
Panelists highlighted the challenges experienced during HRP implementation. Topics included stakeholder engagement, personnel vetting, and unique cultural and/or legislative barriers.
1115-1215
Artificial intelligence and machine learning can be used to enhance information systems security. They can also be used to create sophisticated attacks that evade detection. Presenters shared current research to explore the risks and rewards of emerging tech on insider threat mitigation.
1115-1215
This session used two recent cases of radioactive materials in the possession of people who have explosives knowledge to underline the importance of developing strategies to find possible insiders. Material that has gone missing in the past cannot be assumed to be gone for good. Therefore, minimizing the use of radioactive materials, wherever possible, can prevent the misuse of such material in a dirty bomb scenario.
1115-1215
Novel Approaches to Mitigate Insider Threats, Pt. 2The Critical Pathway to Insider Risk is an empirically based behavior model created by Eric Shaw and the CERT Insider Threat Group. The model is used by numerous insider threat programs to help identify potential risk indicators of malicious insider behavior. This talk covered initial development of the model, studies conducted to validate it, and how insider threat programs use the model operationally.
1115-1215
Geographically diverse panelists shared information about security culture initiatives implemented across a variety of facility types.
1215-1315
1315-1415
CONCURRENT SESSION 2 – Interactive Exercises
1315-1415
Participants with varied backgrounds shared their experiences and views, which provided an overview of prioritized red flags and measures in the topic of ‘observation’. The goal was to evaluate, in small groups, a set of red flags and measures and place them in different categories: high/medium/low and must-have/ nice-to-have/ not useful. This exercise is based on doctoral research. At the end of the exercise, participants reviewed and reflected on their choices as compared to the research. Note: The downloadable cards are to be printed 2-sided: Side 1: Observation, Side 2: Logo.
1315-1415
During this exercise, participants learned how an insider with cyber capabilities can negatively impact facility operations. Real world cases will be examined to illustrate best practices to bolster security cybersecurity programs.
1315-1415
The nuclear power industry faces unique challenges with multinational workforces. On one hand, embracing diversity and multicultural teams can lead to dynamic and inclusive organizational environments. However, diversity can also amplify differences in security awareness, culture, vetting, and qualifications. To broadly address these differences and create baseline levels of security, a Nuclear Security Culture exercise addressed these concerns. The exercise identified unique cultural dimensions associated with nations and combined core components with a strong Nuclear Security Culture.
1315-1415
Do you know how to effectively collect information when a suspected insider threat incident has been reported? Techniques from motivational interviewing research were demonstrated to illustrate what works to reduce resistance and increase information collection.
1315-1415
This interactive, realistic scenario-based experience focused on enhancing awareness and implementing strategies to counteract insider threats enabled by cyber means. The session’s primary goal was to educate attendees about the criticality of recognizing and identifying risks, cross functional communication, and coordination between security domains to develop efficient strategies to mitigate these insider threats.
1415-1445
Coffee Break:ASK AN EXPERT SESSION 3: Cybersecurity Focus Group
1445-1545
CONCURRENT SESSION 3 – Focus on Trustworthiness & Reliability, Cybersecurity, Physical Protection & Technical Measures
1445-1545
Evaluating States’ Implementation of NMAC for Nuclear Security Panelists explored barriers to implementation of IAEA guidance (NSS 25-G and 32-T) on NMAC for nuclear security recommendations.
1445-1545
[Novel Approaches to Mitigate Insider Threats, Pt. 3]
1445-1545
Challenges Regulating and Mitigating Threats for A/SMRsAdvanced and small modular reactors (A/SMR) pose challenges to a country’s existing regulatory framework, especially regarding security requirements. Panelists explored developing and implementing regulations, technology and operating paradigms, and workforce impacts on insider threat mitigation for these new reactors.
1445-1545
Experts from the social and behavioral sciences discussed the contributors to human error and insider threat, including ways to assess the risk of human error (e.g., human reliability analysis), contributing factors to human error, and tools for minimizing the likelihood of human error.
1445-1545
Building effective ways to measure the success of an insider threat program is important to assess whether and to what extent the program has an impact.
1545-1600
Coffee Break & Transition
1600-1700
DOEL-4 IncidentThis session provided a retrospective of the DOEL-4 sabotage case, which occurred in Belgium in 2014. The case study provided in-depth information on what happened, how the threat was mitigated, and investigated. The case study demonstrated the value of a robust security culture throughout an organization.
1700-1800
Investigating and Responding to Insider Threat EventsLaw enforcement and security services experts reflected on their role in preventing, detecting, and responding to insider threats.
1800-1815
Day 2 Wrap-Up/Mentimeter
1815-2000
International Initiatives & Vendor ExpositionSelected organizations and vendors were available to discuss products, materials, and events germane to the insider risk/threat community.
1815-2000
Students & Scholars Poster SessionInterested students and educators were available to discuss their current research with participants.
1815
Adjourn for the day
Thursday, March 7, 2024
Over the Horizon Threats and Solutions; Evolving the Community of Practice
Time
Topic
0900-0910
Welcome; Recap of Day 2 and Preview of Final Day.
0910-1000
Violent extremism has galvanized public fear and attention. The presenters described which factors might increase (risk factors) or decrease (protective factors) risk, how those factors might operate, and how practitioners can prepare risk formulations and scenario plans that inform risk management strategies to prevent violent extremist harm.
1000- 1010
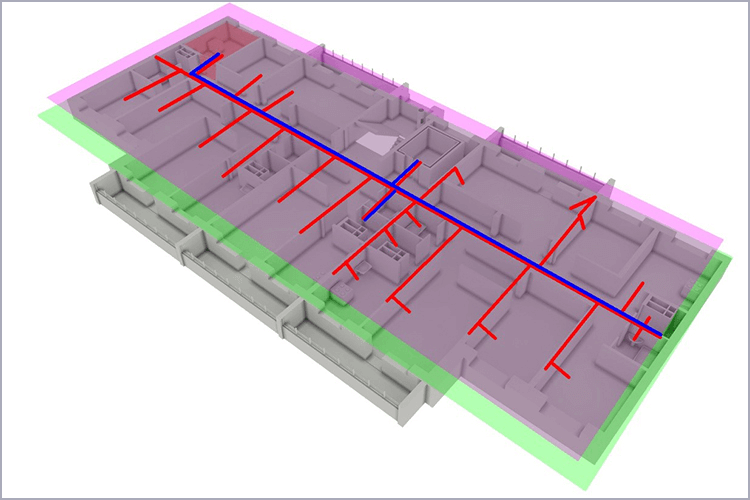
The Integrated Measures Exercise (IME): Introduction
1010-1030
Coffee BreakASK AN EXPERT SESSION 5: Trustworthiness & Reliability Focus Group
1030-1230
Integrated Measures Exercise (IME) Four Breakout Rooms Developed in collaboration with the IWG Steering Committee members, this exercise addressed elements from all five focus groups.
1230-1330
LUNCH
1330-1400
IME EpilogueRepresentatives from each of the small groups shared feedback, and key takeaways were reinforced through discussion and Q&A.
1400-1445
Panelists from academia and research institutes reflected on general theories underlying insider risk and threat, educational programs on the topic, and nascent areas of research.
1445-1515
Coffee Break: International Initiatives & Vendor Exposition Reopens
1515-1600
1600-1645
1645-1700
Closing Remarks & Adjourn
Live Interactive Tabletop Exercises
These interactive sessions provided participants with opportunities to explore true-to-life insider threat scenarios. Working together to identify potential threats and understand insider motives, participants brainstormed mitigation strategies and learned from expert presenters and other symposium attendees.
Lost in Translation: The Importance of Non-Verbal Gestures
Nonverbal gestures and expressions make up an incredible 60-70 percent of human communication! Therefore, cultural nuances and silent signals play a crucial role when determining trustworthiness and reliability.
This exercise explored non-verbal communication while also considering cultural dimensions and common cultural signals. Participants were asked to demonstrate and assess concerning non-verbal behaviors within a fictitious nuclear facility.
Evaluating Red Flags and Insider Threat Mitigation Measures
From recruitment to hiring to ongoing employment, every organization has numerous occasions where it must ward against insider threats. Simply put: no detail is too small to escape close attention!
This interactive activity explored “measures” for assessing observed behaviors and potential “red flags.” Participants worked with their teams to categorize and rank issues to determine when a potential threat is problematic enough that it deserves preventive action.
Cybersecurity for Radiological Facilities
Have you ever wondered what it’s like to be an insider? Well, here’s your chance!
During a realistic insider attack on a fictitious medical facility, you’ll examine a cybersecurity incident from both the defender and attacker’s perspectives. Participants studied best practices and learn how an insider with cyber capabilities can negatively impact operations.
This table-top exercise is a shortened version of an exercise developed by the Cybersecurity Focus Group, and anyone may download the exercise to conduct at home.
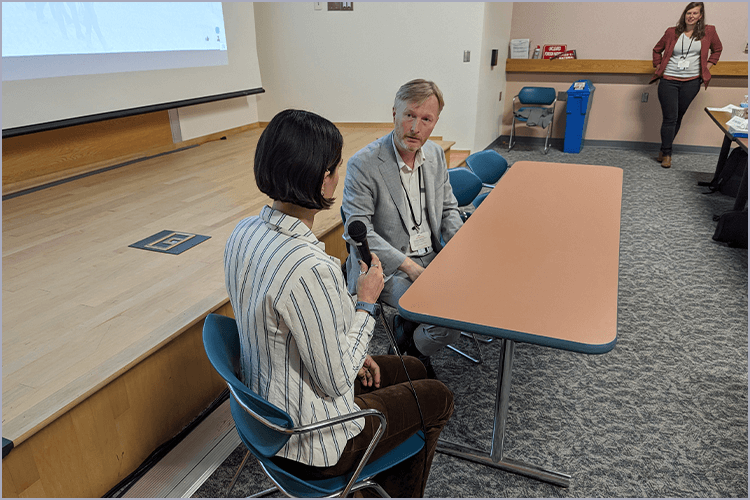
Building Good Rapport in Interviews
During investigative interviews, security professionals need to establish what happened and by whom. Information elicited from interviewees informs the threat assessment and management process. In other words, the better the information, the better the organization’s decision-making process!
Participants explored techniques to build cognitive and affective trust while strengthening active listening and non-coercive rapport-building skills.
The Typhon Intrusion at ARA: Uncover the Insider Threat
Have you ever daydreamed about being in a thrilling cyber-espionage story? Well, wake up and take a dive deep into this simulated but all-too-real incident at a nuclear facility!
Participants practiced fortifying their digital and physical realms, worked on early detection and insider threat recognition best practices, and developed strategies to quickly counter and mitigate damage through rapid response tactics.
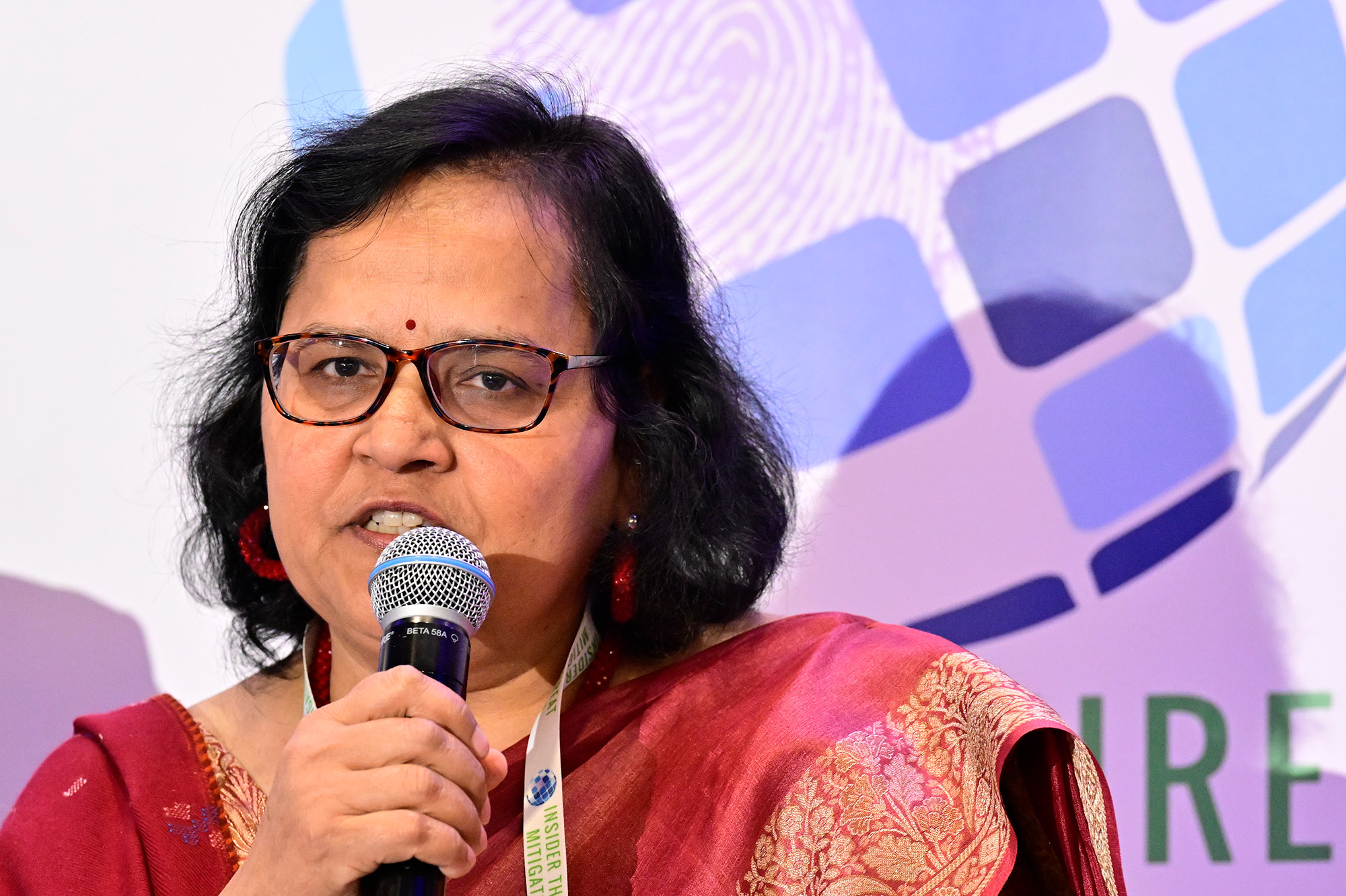
Featured Presenters
The 2024 Symposium brought together leaders in government, industry, and academia to explore priorities and challenges for insider threat mitigation in nuclear security.

Annelies Verlinden
Minister of the Interior, Institutional Reform and Democratic Renewal, Kingdom of Belgium
Prior to becoming minister of interior, Annelies Verlinden was a Co-managing Partner at DLA Piper, an innovative global law firm. While respecting the prerogatives of the competent authorities, she is responsible for the coordination of the general police policy and the coordination of the management of the federal police and the local police. Her policymaking in home affairs includes civil security, the support of the prevention and security policy of municipalities, private security, registration and updating of the national register of intelligence regarding Belgian nationals. Verlinden has a degree in law from the University of Leuven and completed the leadership program at Harvard Business School. Learn more about Annelies Verlinden

Jill Hruby
Under Secretary for Nuclear Security and NNSA Administrator, United States Department of Energy
Jill Hruby leads the U.S. Department of Energy's National Nuclear Security Administration (DOE/NNSA) in achieving the nation's nuclear security missions by ensuring the nuclear security enterprise is bringing cutting-edge science and creativity to sustain and fully understand the U.S. stockpile without testing; providing new technologies and procedures to lower cost and reduce the time to deliver all mission requirements; staying ahead of adversaries; and developing advanced capabilities to enhance nuclear security, arms control, and Navy reactors. Hruby previously served as Director of Sandia National Laboratories and has mechanical engineering degrees from Purdue University and the University of California at Berkeley. Learn more about Jill Hruby

Yvan De Mesmaeker
Secretary General for the European Corporate Security Association (ECSA)
Yvan De Mesmaeker founded Omega Risk, an independent audit and consultancy practice, advising major international corporations and organizations on security, resilience, anticipation and assisting them with strategic networking. Subsequently, he was appointed Secretary General of the European Corporate Security Association (ECSA), a not-for-profit professional association of managers and officials in charge of the security and resilience of corporations and national, EU, and international institutions. De Mesmaeker graduated as a civil engineer (academic degree between a MSc and a PhD) from the Free University of Brussels and studied finance and international marketing at a post-academic level (studies in Dutch, French, and English). Learn more about Yvan De Mesmaeker

Frank Hardeman
Director General of the Federal Agency for Nuclear Control, FANC, Belgium
Frank Hardeman has served as Director General of the Federal Agency for Nuclear Control (FANC) since 2018. FANC’s mission is to promote the effective protection of the general public, workers, and the environment against the hazards of ionizing radiation. Prior to his work at FANC, he held various positions at the Belgian Nuclear Research Centre (SCK CEN, MOL), including Deputy Director General; Head of the Environment, Health, and Safety Institute; Head of the Health and Safety Department; Head of the Society and Policy Support Unit; and Head of Nuclear Measurement Laboratories. Hardeman has degrees in nuclear physics, nuclear engineering, sciences, and industrial safety from the University of Leuven.